The Corellium Resource Library
The latest articles and news on mobile app security testing, IoT and research from Corellium and community contributors.

Steven Smiley & Brian Robison •
Apr 30, 2024
Mobile Vulnerabilities Exposed: Data in Transit
Learn how to capture network traffic and protect data in transit. Watch our expert webinar or read the recap and case study.

Corellium •
Apr 26, 2024
Deep Dive into Experimenting with Messaging App Vulnerabilities
Marco Chomut of TFP0 Labs dives deep into experimenting with messaging app vulnerabilities in our latest webinar. Watch today.

Chris Williams •
Feb 29, 2024
Introducing MicroSnapshots - Leveraging copy-on-write memory
Join Corellium for a demo showcasing our MicroSnapshots feature, designed for rapid restoration of a virtual machine's state, ideal for snapshot fuzzing.

David Manouchehri •
Feb 09, 2024
Corellium with AI
Automate Complex Tasks by Giving GPT-4 Control over Corellium’s API.

Chris Williams •
Feb 05, 2024
Corellium CoreSight Tracing Demo
Join Corellium for a CoreSight Tracing demo. Explore capabilities that provide insightful analysis on program flow/coverage, system calls, and more for user space processes.

Dan Thagard •
Dec 20, 2023
Understanding Terraform and Corellium: A Perfect Match for Virtual Device Management
Discover how combining Corellium with the power and flexibility of Terraform can streamline virtual device management for development and testing teams.

Chris Williams •
Nov 06, 2023
Using Corellium Kernel Hooks to Disable Exploit Mitigations
In this technical article, we'll take a look at a vulnerability in XNU, the kernel used by iOS and macOS, and explore how Corellium kernel hooks can help to disable exploit mitigations.

Chris Williams •
Nov 06, 2023
Exploring UNIX pipes for iOS kernel exploit primitives
Explore the use of UNIX pipes for iOS kernel exploit primitives in this insightful technical article. Learn how Corellium's magic can be used to practice and develop exploits without relying on vulnerabilities.
Brian Robison •
Oct 30, 2023
Mobile Malware and Threat Research Without Limits
In this article, we look at several types of mobile malware — of increasing sophistication — and discuss opportunities for research and analysis using virtual devices.

Brian Robison •
Sep 14, 2023
Deep Dive into Reverse Engineering on Android
Learn the tools and tactics needed to optimize your approach to Android reverse engineering. Watch our expert webinar or read the recap and case study.

Rob Ferri •
Sep 07, 2023
Brute Forcing PINs with Frida: Mobile Penetration Testing
Walk through mobile penetration testing on a 2FA application that resulted in the creation of a Frida script to brute force hardcoded values.
David Manouchehri •
Aug 28, 2023
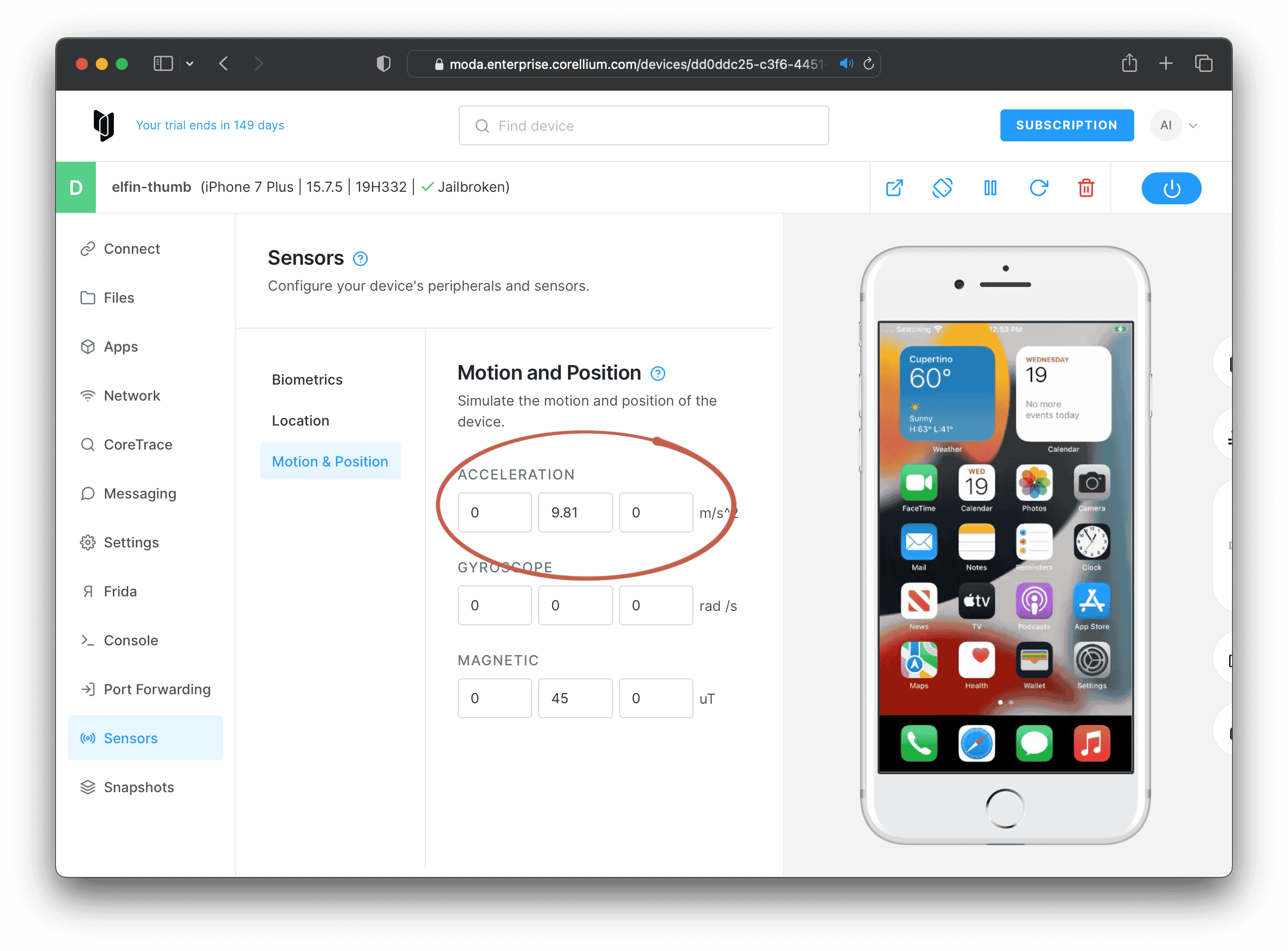
Taking Off with Golang: An Introduction to the Corellium API Bindings for Go
Corellium simulated changing the accelerometer of an iPhone using Corellium API bindings for Golang, an example of simulating the real world with Corellium and Golang for iOS.
Subscribe to Stay Connected
Keep up to date with emails for the latest product news and technical articles.
